Digital sobriety, influence of software
The ecological and societal impacts of the digital sector are a reality, all the more obvious for the physical part of our equipment. What is the role of software in this equation?
Digital sobriety is the practice of measuring and reducing how we use digital services. The problem has been clearly identified for terminals, which collectively represent 2/3 of digital impacts: their lifespan must be extended. But what does the remaining 1/3 represent and what are its characteristics?
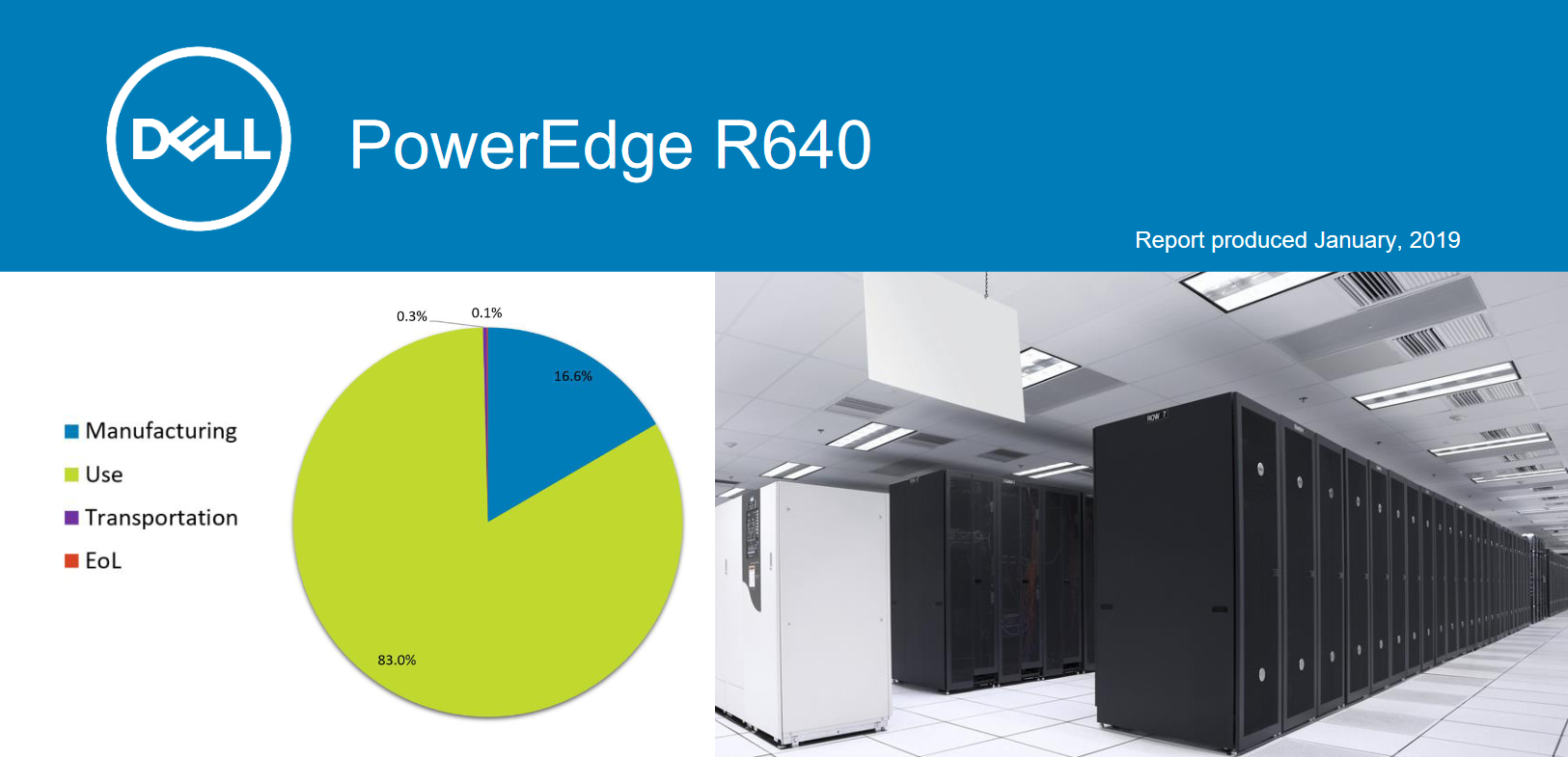
The analysis of the complete life cycle of our IT equipment sheds light on the main vectors of pollution: 80% linked to manufacturing.
However, this ratio is reversed for the remaining 1/3 which includes networks and datacenters: 80% of the impacts linked to usage. The software components that use these resources play a key role in limiting and reducing those impacts.
Ban the useless
According to a March 2022 report published by McKinsey, only 20% of applications running in the cloud are used frequently enough to justify the cost of their 24-hour availability. The remaining 80% of applications are rarely used or even unused for long periods.
These apps consume valuable resources that could be freed up and used by active apps. In this sense, "serverless" type architectures are an interesting approach, but their current implementation by the largest actors is far from optimal.
What is the digital sobriety of software?
By acting on several complementary factors, it is a way of reducing the resources consumption of digital services. Increasing the efficiency of necessary operations and minimizing the resources of inactive services, even temporarily.
On closer inspection, it is also a huge vector for saving infrastructure and energy costs in datacenters!
Key factors
- Focus on the business by creating the conditions for a close relationship between IT management and users. In other words, respond adequately to an identified and justified need.
- Optimize development and IT intervention time thanks to a more agile structure and methodology.
- Reduce the use of IT resources by limiting unnecessary functionalities and the massive import of uncontrolled third-party components.
- Favor modular IT architectures and resources, which offer greater integration flexibility when new needs or new tools emerge.
- Strengthen cybersecurity by keeping control of the IT infrastructure and increasing ownership of the code and tools.